Do you know what the first computer password was? Wired asked that question in 2012. They never actually answered it, and of course, the answer is not very important. But the story behind the invention of the computer password is still instructive.
According to the Wired story, the first well known example for using passwords to access computer files was in the ’60s, on the CTSS computer operating system, developed at MIT. Specifically, the credit goes to Fernando Corbató, who is quite blasé about the matter:
“Surely there must be some antecedents for this mechanism […] Putting a password on for each individual user as a lock seemed like a very straightforward solution.”
I became interested in this story while working on the signup and onboarding experience on WordPress.com. Some of the patterns that make up the process are so common and familiar, we may take them for granted. I wanted to go back in time to when these patterns first emerged. Basically, I wanted to find the original design document for the username and password.
I never found it – obviously, it never existed. And imagining that it did wasn’t the only anachronism I was guilty of. I was hoping to find screenshots that demonstrate how these early time sharing computers worked. But in this demonstration of time-sharing by Corbató, the whole interaction happens on a typewriter…
The entire video is worth watching, but the actual demonstration starts at around 18:30.
The problem Corbató had to solve seems like a user problem – it served users’ need to have personal files that only they can access. But early computer users didn’t really care about security very much, as evidenced by the countless tales of password shenanigans that accompany every account of computers in this period. And they never had a problem knowing who they were and who they weren’t. The computers were the ones who needed help with that.
What eventually became the “User Account” is just how we first taught computers to tell us apart from each other. And we’re still using the exact same model today, the same interaction patterns, down to the terminology.

Going by Corbató’s comments, this wasn’t exactly designed. The design emerged, rather than being deliberately created. Yet, passwords weren’t the only available solution, and other ideas were considered or tried. For example, relying on personal knowledge: asking you a question that you would already know the answer to, and that no one else is likely to know too (like your mother’s maiden name).
This may have improved the user experience, since one wouldn’t have to learn an arbitrary password. But it’s much easier for a computer to remember an arbitrary password than a long list of personal facts, and this solution was chosen.
Iterate: Intuition is grounded in interpretation through iteration.
Iteration, put more simply, means “repetition”. As a motto for good design, “repetition” doesn’t sound promising. Isn’t the definition of a function that for each input, there is exactly one output? What would be the point of repeating it?
The point would either be to change the function of design, or to change the input that feeds it.
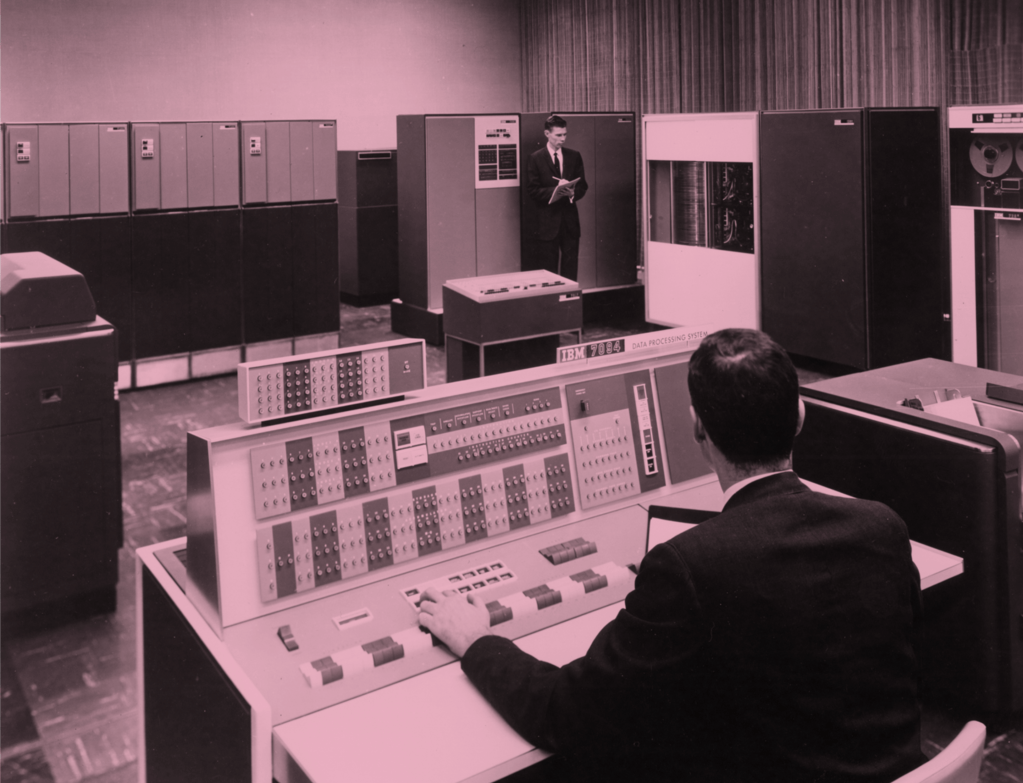
Image at the top of IBM 7094 computer which ran the CTSS operating system taken from Compatible Time-Sharing System (1961-1973) Fiftieth Anniversary Commemorative Overview (PDF link)